Essential Characteristics Of Cryptocurrency
Introduction
A bitcoin is electronic or digital money protected by encryption, making counterfeiting and double-spending practically unfeasible. Several cryptocurrencies like bitcoins are built on distributed ledger technology, a digital database maintained by a well-organized computer network. Bitcoins are distinguished because they’re not being produced by any centralized power, making them potentially impervious to government intervention or manipulations. To know more about how to invest and trade in bitcoin, Bitcoin Loophole will guide you.
- Trustless
Bitcoins seem to be insecure as it was created to require no one to trust anyone else for the organization to operate before bitcoin. Each type of money needed you to accept a centralized body to utilize it. That central power represents the key vulnerability that contributes to the currency’s collapse in all circumstances. With bitcoins, each component of the network verifies what the others say without relying on anyone. When you make a bitcoin payment, it is received by all miners, who check the signature for validity. In case the signature is false, the payment is discarded.
Since everybody on the system has a blockchain version, we no longer have to believe a certain third party since we could check it against another database. And besides, you already have duplicate record details. Blockchain technology is a type of decentralized database. Since we are yet to work out just how we employ bitcoins and whether or not they are here now to remain, they are all here to maintain a presence. Apart from the various key advantages of bitcoins and distributed ledger technology, resolving the centralized trust problem is a significant breakthrough to ensure that crypto has a long-term future.
2. Immutable
Three concepts should govern immutability in cryptocurrency exchanges:
- Rewriting history ought to be incredibly unlikely or impossible.
- Those without access to the secret code should be unable to send money.
- On the distributed ledger, every payment is documented.
We examine our transaction information with the financial institution to see how much money was spent from our banking accounts. We entrust our financial institutions to execute our operations to receivers without fabricating transactions or manipulating our money. If illegal transactions take place, the financial institution should be authorized to correct the problem. Because the characteristics of centralization and confidence have been eliminated from cryptocurrencies, there isn’t any more a foreign entity to whom we can entrust these tasks. As a result, transaction data are publicly available to the public and are therefore not editable. Though changing the transactional record is not unfeasible, cryptographic encryption makes it very difficult. It necessitates compromising the entire bitcoin system.
3. Decentralized
Because “decentralization” is a popular concept in the crypto field, it’s critical to describe it thoroughly. It can have a variety of connotations. “Since they are essentially centralized, distributed ledger technology is formally decentralized, without any single point of failure, and practically decentralized, without any single point of structural failure. There is a single agreed-upon state, and the system functions as a single device.”
- Failure Tolerance: Since a decentralized system depends on connections of different parts, they are much less prone to failure by mistake.
- Attack Opposition: Since decentralized networks lack weak central locations that could be targeted at a lower price than the entire network, they are much more costly to assault, demolish, or control.
- Collusion Aggression: In decentralized networks, it is more difficult for individuals to behave in activities that enhance them at the cost of others. On the contrary extreme, businesses and authorities frequently collaborate in ways that profit them while harming others.
Using mints and inflation rates, state banks and authorities regulate the production and creation of wealth.
Conclusion
A bitcoin that aims to join the mainline financial sector must meet a variety of requirements. It will indeed have to be computationally intensive (to prevent theft and cyberattacks) but simple to comprehend for customers; decentralized but now with sufficient customer protections and protective measures; and maintain data confidentiality without serving as a duct for evading taxes, laundered money, and other criminal events.
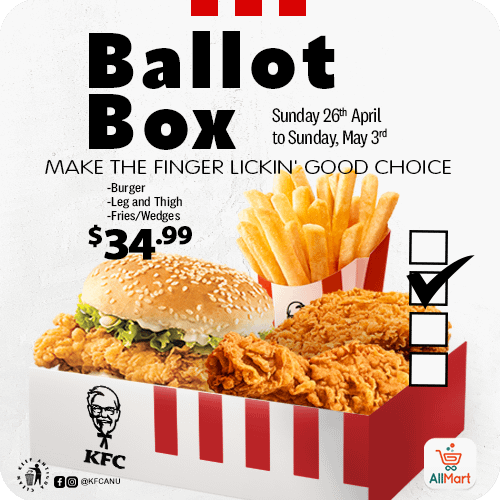
Advertise with the mоѕt vіѕіtеd nеwѕ ѕіtе іn Antigua!
We offer fully customizable and flexible digital marketing packages.
Contact us at [email protected]